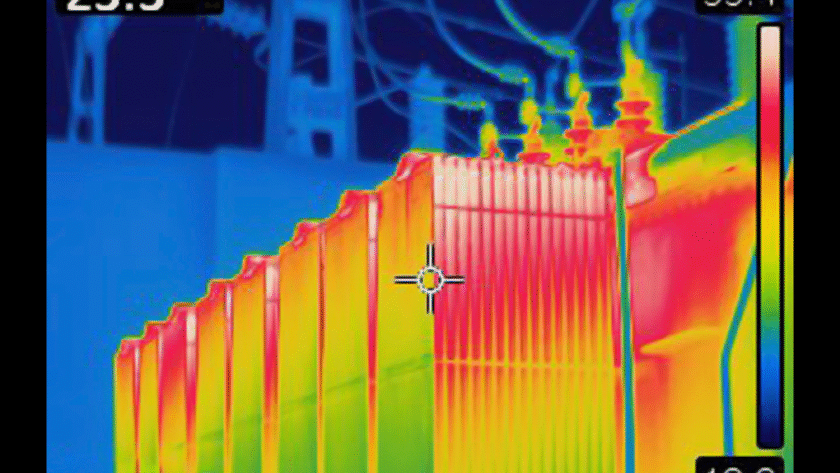
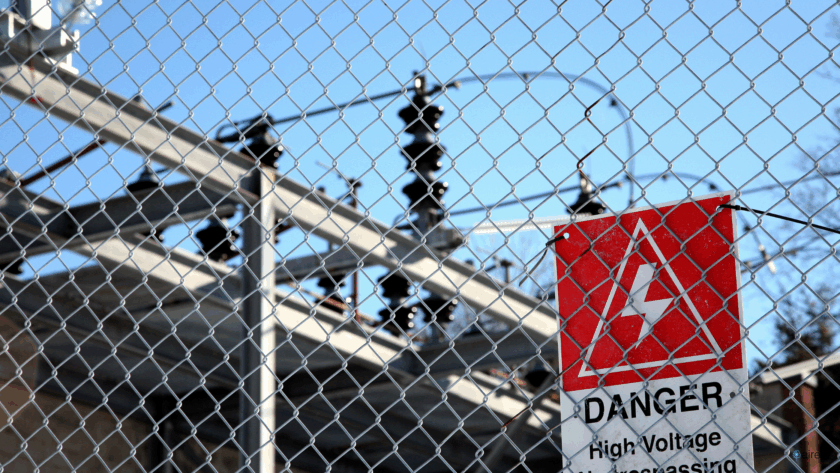
It is 3:00 AM. An alert triggers at a remote electrical substation 45 miles outside of town. The legacy camera system has detected "motion" along the perimeter fence.
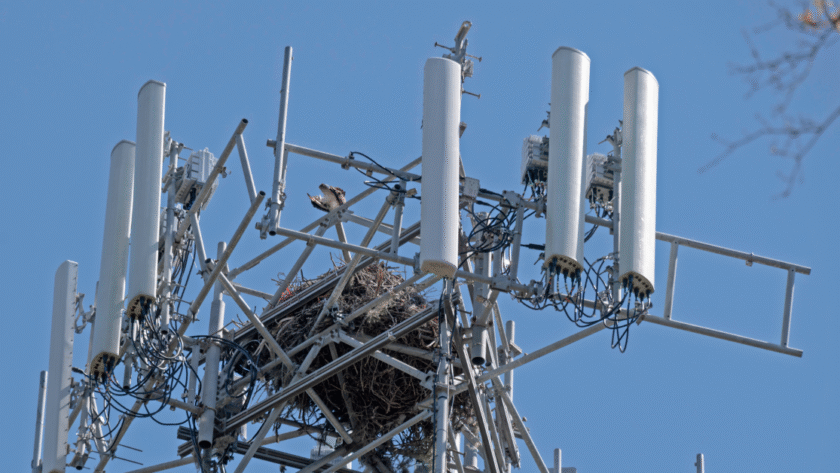
The operator in the Security Operations Center (SOC) squints at a grainy, low-light video feed. They can't tell if the movement is a sophisticated copper thief cutting…